With fears of the global COVID-19 outbreak increasing daily, more businesses than ever are looking to give their employees the option to work from home. But a bad remote access implementation can pose a greater threat to your company than a global pandemic. Security vulnerabilities, poor configurations, and infected employee devices are all risks that need to be considered when planning for a remote workforce.
Attackers and criminals are actively exploiting the rise in remote workers, according to a recent alert from the Cybersecurity and Infrastructure Security Agency (CISA), a part of the Department of Homeland Security (DHS).
The Basic Problem
Most organizations concentrate their cybersecurity defenses – firewalls, anti-virus and the like – at the edge of their network. This is known as “perimeter defense”, and it works well when an organization’s compute resources are entirely on-premises. Remote workers, however, require a “hole” in the perimeter defense as they will likely require access to files and other resources behind the firewall.
Having a large number of remote workers greatly diminishes the effectiveness of perimeter defense. Just as a single infected person can transmit coronavirus to dozens of others, a single infected employee laptop connected to your internal network can spread to other workstations, servers, and more. An employee’s personal laptop tends to be less secure than a company-owned and managed computer, amplifying the risk.
The RDP Nightmare
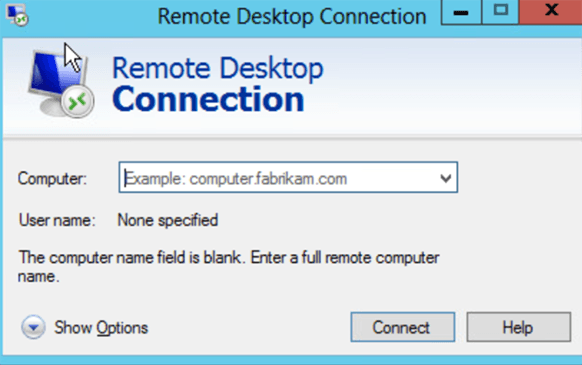 One of the most common methods of providing remote access has been Microsoft’s Remote Desktop Protocol. This tool has been built into different versions of Microsoft Windows for years, making it an easy option. Unfortunately, it also suffers from a number of security vulnerabilities. RDP has become a favorite infection vector for Ransomware, including the highly potent Ryuk strain that’s been crippling everything from government agencies to large corporations. By some measures, RDP was the top mechanism by which ransomware spread in 2019. The risks from this protocol are so great that when we perform a Cybersecurity Assessment for our clients, we raise an automatic red flag when we see it enabled.
One of the most common methods of providing remote access has been Microsoft’s Remote Desktop Protocol. This tool has been built into different versions of Microsoft Windows for years, making it an easy option. Unfortunately, it also suffers from a number of security vulnerabilities. RDP has become a favorite infection vector for Ransomware, including the highly potent Ryuk strain that’s been crippling everything from government agencies to large corporations. By some measures, RDP was the top mechanism by which ransomware spread in 2019. The risks from this protocol are so great that when we perform a Cybersecurity Assessment for our clients, we raise an automatic red flag when we see it enabled.
It is possible to increase the security of RDP, but with a variety of other options that do the same thing, we recommend against its use in almost all cases.
VPN With Care
Another common method of providing remote access to company resources is a Virtual Private Network (VPN). A VPN essentially provides a “tunnel” from the outside world into your internal network. While this allows users to access all the tools and resources on the internal network, it can also act as a backdoor for attackers.
Your employees’ personal devices may not be set up as securely as your company computers. If an employee device is infected or compromised and connects to your internal network over a VPN, all of your internal systems, files, and resources could be at risk.
Weak or re-used passwords are another common issue with VPNs and remote access in general. If a cybercriminal can easily guess the login credentials for one a of your employees, they may be able to silently gain access to your network and carry out additional attacks. To mitigate this, the CISA recommends that all VPN implementations be secured with Two-Factor Authentication (2FA).
Collaboration Tools Pose Hidden Dangers
Collaboration tools like conferencing software and chat platforms are essential for a remote workforce, but if you’re not regularly updating your software you could be at risk. Major vendors like Cisco WebEx, Zoom, and Slack have had highly dangerous bugs that could allow attackers to remotely install software on a victim machine, spy on users by remotely activating the webcam, or hijack and redirect file downloads. Though collaboration software seems pretty innocuous, it needs to be regularly updated like everything else.
The Cloud Doesn’t Mean Your Safe
Companies that rely on cloud services like Office 365 and Dropbox may have to worry less about software vulnerabilities, but unauthorized access is an issue no matter where your data is located. Again, infected employee devices and compromised accounts are key attack vectors to worry about. Misconfiguration is another common security issue, as many cloud services are set up to provide public or global access by default.
What You Can Do
Giving your workers the option to work from home doesn’t have to come at the expense of your company’s security. Basic cyber hygiene practices – strong passwords, secure configurations, and regular software updates – go a long way towards staying safe. Any remote access implementation should also be using Two-Factor Authentication (2FA) to guard against stolen passwords and compromised devices. VPN security can be further enhanced through the use of digital certificates instead of usernames and passwords.
Ensuring your employees are connecting from up-to-date, properly configured devices is crucial. Duo Security, one of our partners, has a great way of doing this as part of their 2FA platform. You can block access from devices that aren’t secure, and force workers to fix any security issues before access is granted. Other options include managing employee devices through a Mobile Device Management (MDM) or endpoint management product like Microsoft Intune, though this can increase the burden on your in-house IT staff.
All of your employees should be receiving some form of security awareness training. Attackers are actively exploiting the fear of COVID-19 to spread malware through phishing campaigns. Make sure your remote workers can spot a phony CDC warning or bogus list of Coronavirus Safety Measures.
And, as always, backup your data! Good backups can ensure your business will survive any disaster, be it a cyberattack or global pandemic.
If you’d like helping securing a remote access implementation, check out our remote worker solutions to contact us!
